
By Errikos Andreakos, Chief Commercial Officer for MarTrust, at Marcura
A growing concern
Maritime cyberattacks doubled in 2025 according to CYTUR’s 2026 Maritime Cyber Threat White Paper. For finance and compliance teams, payment fraud, particularly Business Email Compromise (BEC), is the most immediate and measurable financial risk within that broader trend.
BEC and payment fraud targeting maritime organisations runs three to five times higher than traditional banking when adjusted for transaction volume. The reasons lie in how the industry operates.
Why maritime is structurally exposed to payment fraud
Shipping combines high-value transactions with decentralised decision-making and limited verification infrastructure. Even where vendor relationships are long established, most operators lack the means to confirm that the counterparty communicating today is the same one originally onboarded.
Familiarity lowers vigilance. BEC attacks exploit precisely that gap.

Fraud Risk = Exposure × Verification Gap × Time Pressure
Most operators screen vendors at onboarding. The vulnerability emerges afterwards, when bank details change between registration and payment. In contrast to retail banking, where modest transactions of a few hundred dollars often require secondary approval, maritime organisations routinely authorise five-figure payments at first pass.
Legal and commercial pressures compound the risk. Agents can hold a vessel for non-payment, triggering demurrage and cascading delays that quickly exceed the value of the invoice. Shipping companies pre-fund to avoid disruption. Fraudsters understand this dynamic. Once funds clear, recovery is unlikely.
A vessel operator receives a prefunding request of $85,000. Bank details have been updated due to a compliance issue. Payment is made within hours to avoid delay. Two days later, the genuine agent confirms no funds received. The vessel is held. Total cost exceeds $250,000.
Anatomy of an attack
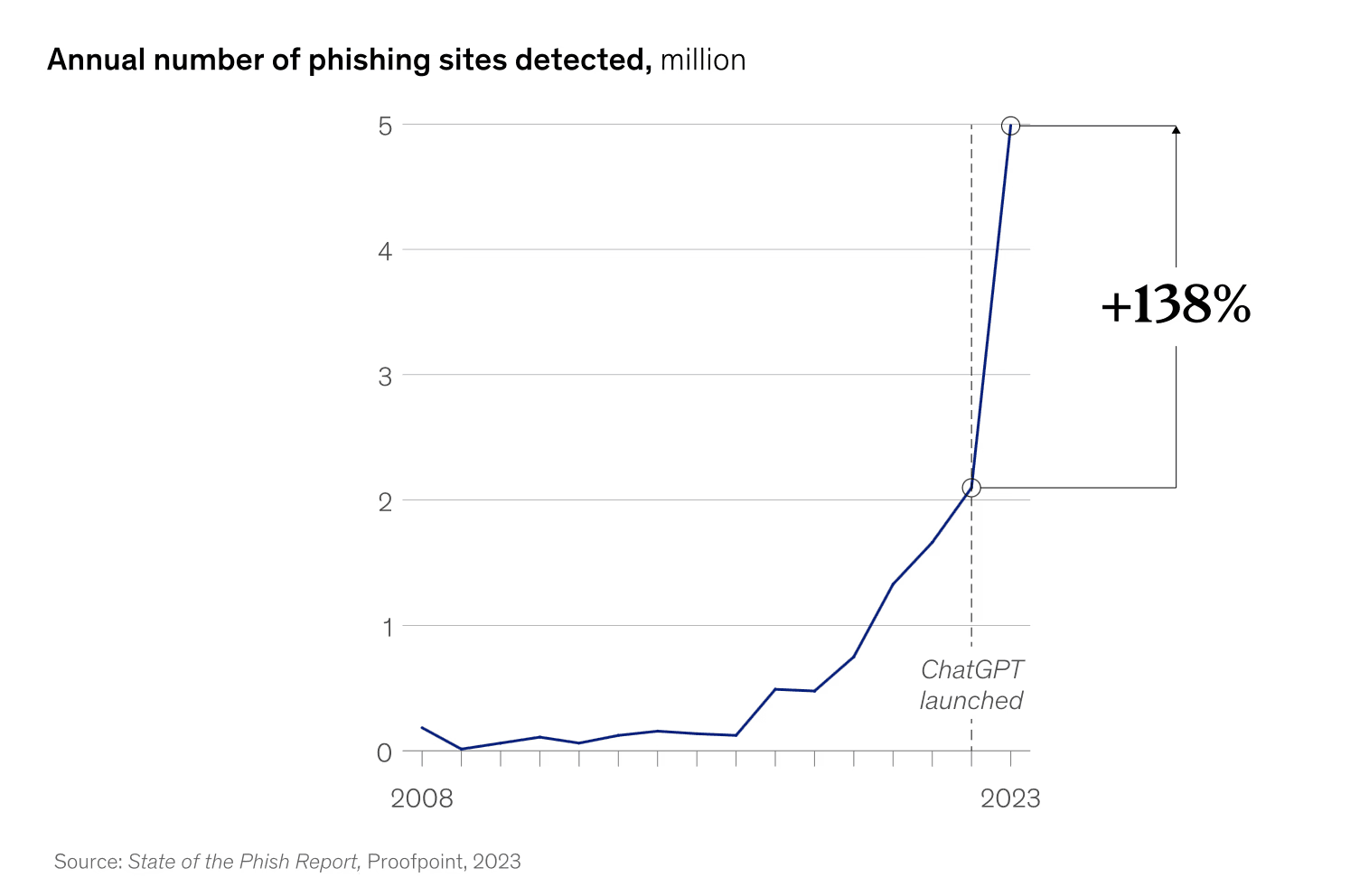
Port agents, often small operations using standard email systems, are a soft target. Gaining access to an account requires little sophistication. A cloned website can be created in minutes using generative tools; a convincing phishing email from that domain is often sufficient to capture credentials.
Once inside, the fraudster waits.
When a prefunding request is issued, they insert themselves into the communication chain by creating a near identical email address. The narrative is plausible: a temporary banking issue, a compliance check, a request to reroute funds.
The attacker already understands the company’s payment thresholds and calibrates the request accordingly. Banks process payments by account number, not name. Discrepancies pass unnoticed.
By the time the genuine agent follows up, funds have typically moved through multiple accounts and jurisdictions. Recovery is rare.
Although port agents are the most visible vector, the same vulnerability extends across the vendor ecosystem: spare parts suppliers, technical service providers and contractors. The pattern is consistent; the outcome is the same.

Instant, trusted, and transparent payments for maritime
Purpose-built for shipping companies, port agents, and maritime vendors delivering instant, transparent, and compliant payments across the globe.
What effective controls look like
No fraud system is foolproof. Models learn from past behaviour; attackers adapt. Software can flag anomalies, but it cannot replace judgment. Organisations that remove human verification altogether are often the most exposed.
The most important control is bank account change management. Any request to change payment details stops immediately. It doesn't matter how plausible the reason sounds. The payment goes on hold and someone calls the contact number registered at onboarding. Nothing moves until the right person confirms verbally.
The second control is bank account validation at the point of payment. verifying on every transaction that the receiving account matches the one registered, and that it hasn't changed since the last payment run.
Marcura does this across $17 billion in annual payments. Over nine years, that combination has stopped approximately 150 fraud attempts, protecting around $10 million in customer funds.
That control operates within the existing payment infrastructure. The deeper answer sits upstream of it entirely.
Removing the attack surface
Business Email Compromise relies on a single weakness: that payment details can be altered without detection. Marcura Pay addresses this at the architectural level by providing a closed payment network.
Each vendor is issued with a dedicated account on the Marcura Payment Network. That account becomes the payment destination. Payments move within a closed ecosystem where both sides of every transaction are known, verified, and fixed.
There is no external bank account to verify, no details to change, and no impersonation attack that can introduce an alternative, drastically reducing the risk of fraud.
The only remaining question is whether maritime operators want to continue trying to manage a known fraud risk or remove the biggest vulnerability from the equation.
Business Email Compromise relies on a single weakness: that payment details can be altered without detection. Marcura Pay addresses this at the architectural level by providing a closed payment network.

Marcura reduces reliance on traditional banks that often delay payments due to manual checks, time zone differences, or missing documentation.
Is preventing payment fraud a priority for your business?
Read more
recent news
Posidonia 2026
Win an Apple Watch Series SE 3.
Enter the Marcura draw. Winners announced live in Athens. Entries close 5th June 2026.









